VirusTotal
@virustotal
Followers
31,568
Following
0
Media
154
Statuses
368
Explore trending content on Musk Viewer
México
• 1560532 Tweets
Morena
• 835665 Tweets
casilla
• 770135 Tweets
Xóchitl
• 481916 Tweets
CDMX
• 367894 Tweets
The Loyal Pin is Coming
• 361337 Tweets
PREP
• 295230 Tweets
AMLO
• 206407 Tweets
El INE
• 180404 Tweets
増山さん
• 65765 Tweets
増山江威子さん
• 62112 Tweets
ルパン三世
• 51939 Tweets
Otros 6
• 32468 Tweets
#FraudeElectoral
• 30002 Tweets
Kaveh
• 27176 Tweets
ゲリラ豪雨
• 20838 Tweets
SmangatPRABOWO UntukNKRI
• 19538 Tweets
KitaKOMPAK KitaKOKOH
• 18781 Tweets
肺炎のため死去
• 16481 Tweets
カーヴェ
• 13915 Tweets
グッズ・ボイス販売
• 12953 Tweets
あなたの運命のライバー
• 10863 Tweets
#MondayMotivation
• 10434 Tweets
Last Seen Profiles
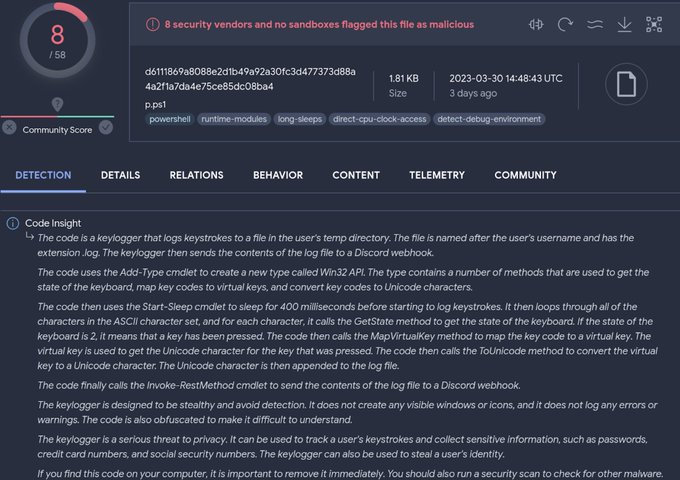
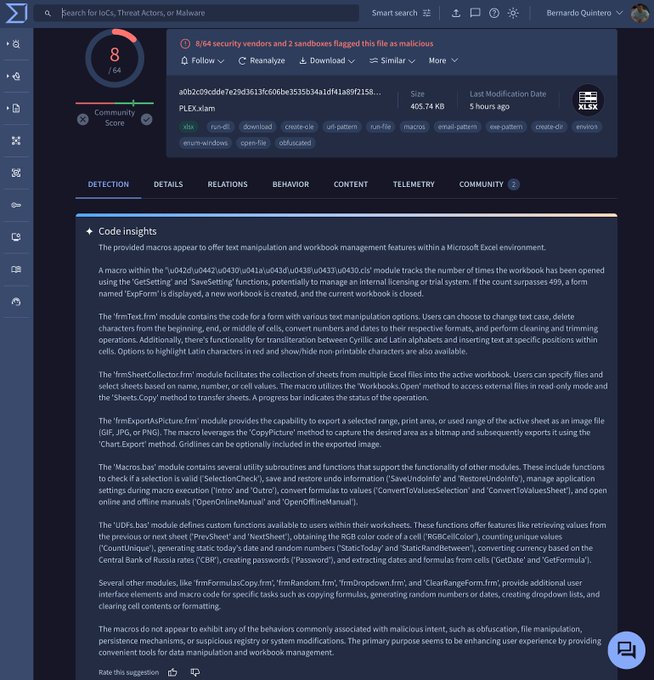
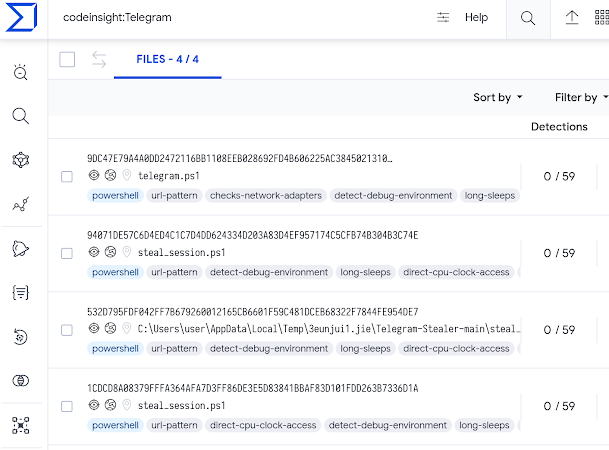
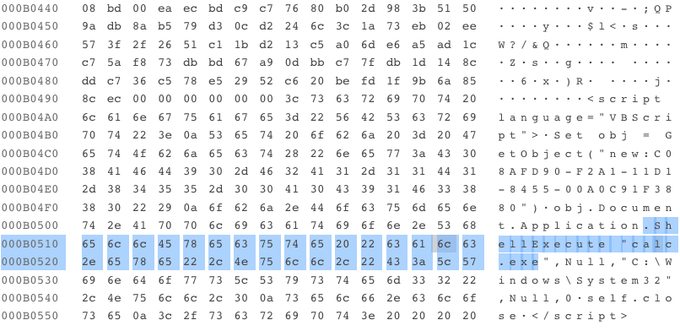
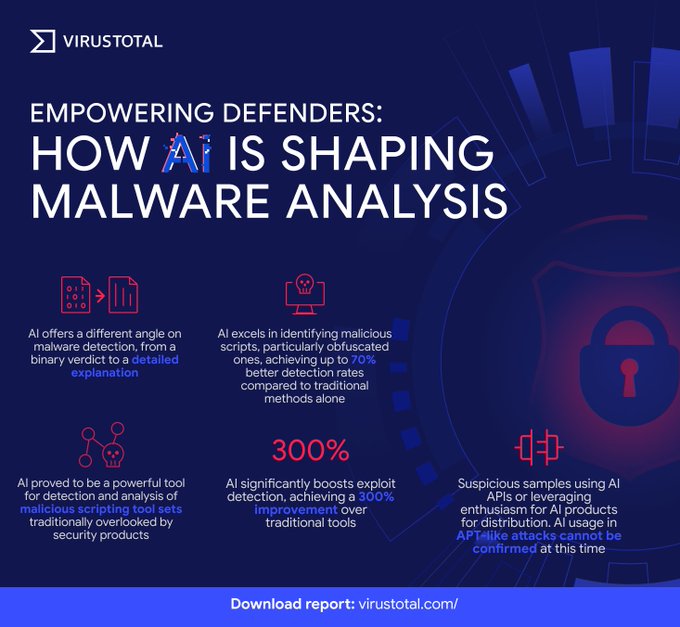
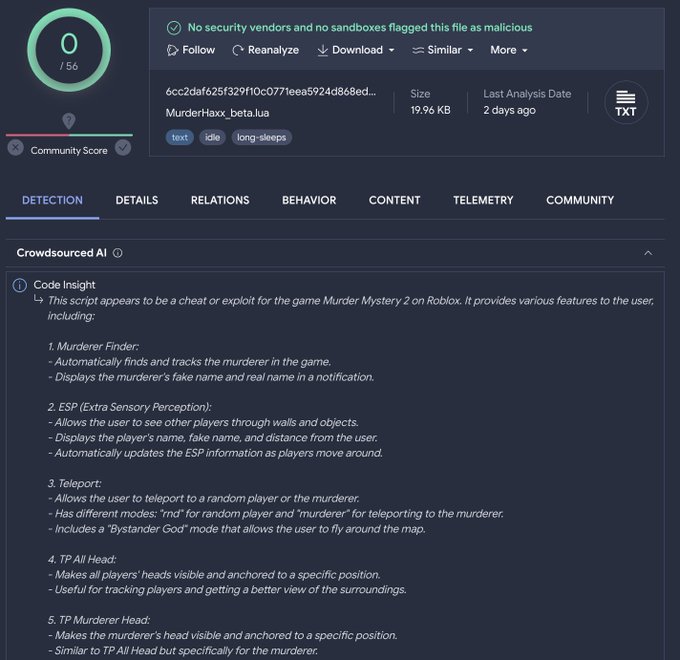
Introducing VirusTotal Code Insight: empowering threat analysis with generative AI. This tool is based on Sec-PaLM (LLM) and helps explaining behavior of suspicious scripts. Code Insight is available now for all our users! More details by
@bquintero
:
10
546
2K
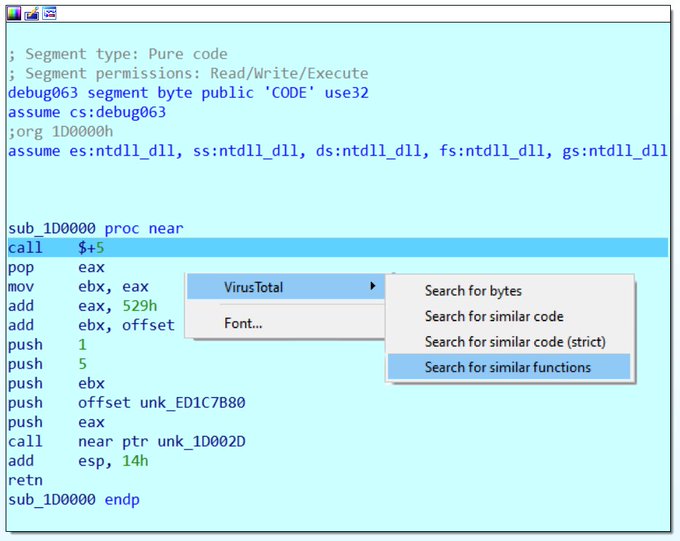
Good news all
#IDAPro
and
#GHidra
fans! Learn everything about VirusTotal's plugins and how to use them in our
"When you go fighting malware don´t forget your VT plugins” blog post by
@gerardofn
5
189
471
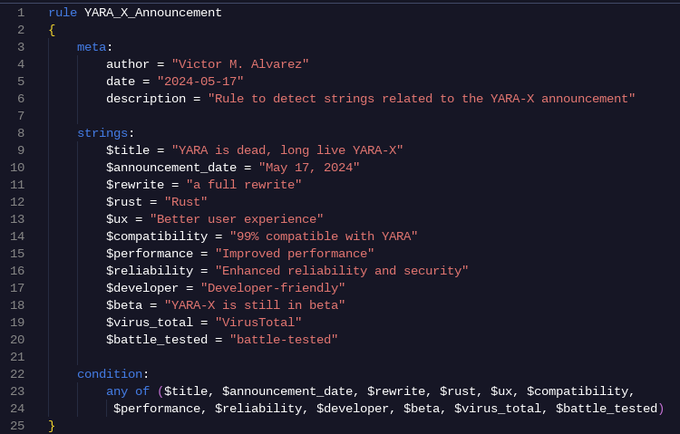
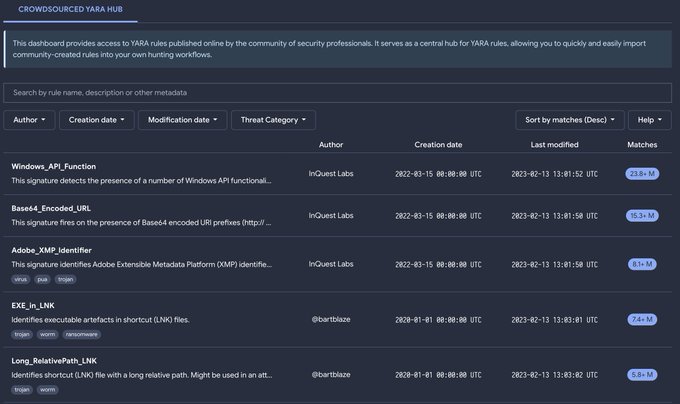
"YARA is dead, long live YARA-X!" 🎉
After 15 years, YARA gets a full rewrite in Rust, bringing enhanced performance, security, and user experience.
Dive into the details in latest blog post by
@plusvic
:
3
177
437
Many of you asked for this, and today we are happy to announce the release of our VTI Cheat Sheet with hints and examples on the most useful VT Intelligence queries and modifiers.
@alexey_firsh
provides all details along with several examples here:
1
153
347
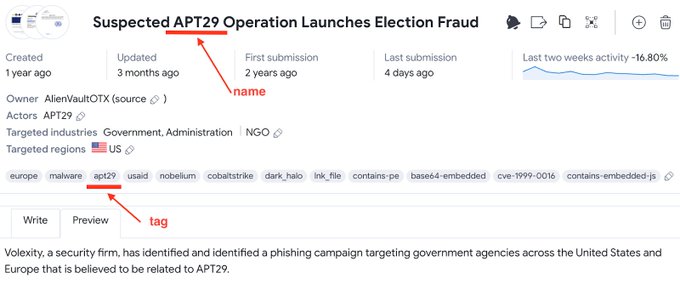
Today we announce YARA Netloc, a new feature extending YARA's supported entities from traditional files to network infra, including domains, URLs and IPs. This opens endless possibilities for hunting and monitoring. All details here, by
@leximagination
:
2
134
280
New VT Academy training for SOC and IR analysts, led by
@digihash
! Learn how to efficiently and successfully investigate and contextualize any malicious activity. Watch now:
0
95
275
In late 2022 we started monitoring PyPI, the most important Python repository. In a few weeks, we found dozens of suspicious packages. Here is our deep dive into PyPI hosted malware, by
@alexey_firsh
:
2
122
273
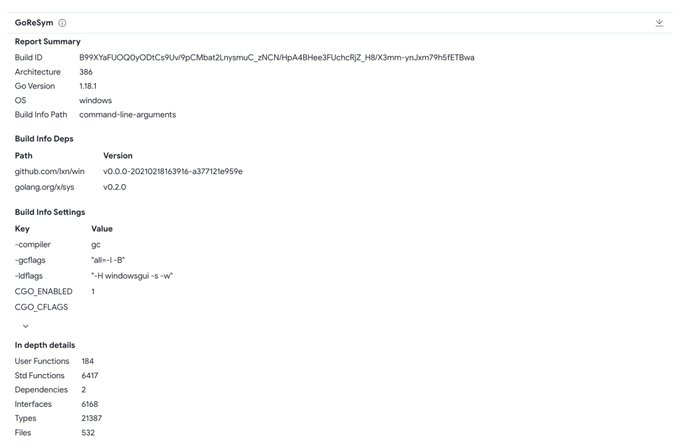
We welcome
@Mandiant
's CAPA and GoReSym to our malware analysis suite. CAPA provides valuable TTPs, and GoReSym produces all kind of metadata to analyse GO samples:
4
83
263
Good news for all the infosec community. Now you can Export/Import VT Collections into/from MISP Events 🎉 by
@thetravelr
4
92
249
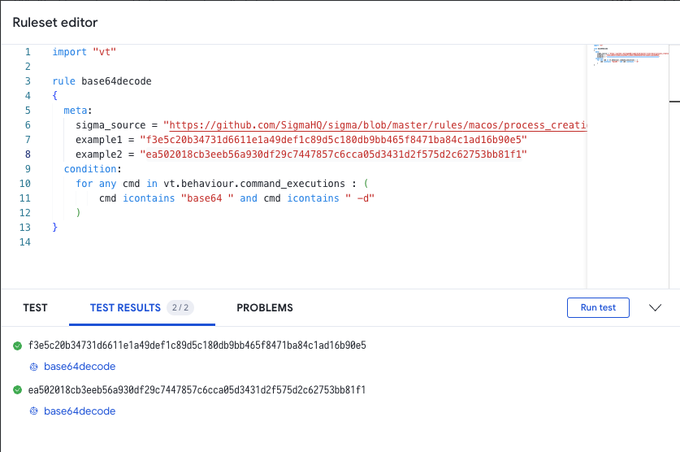
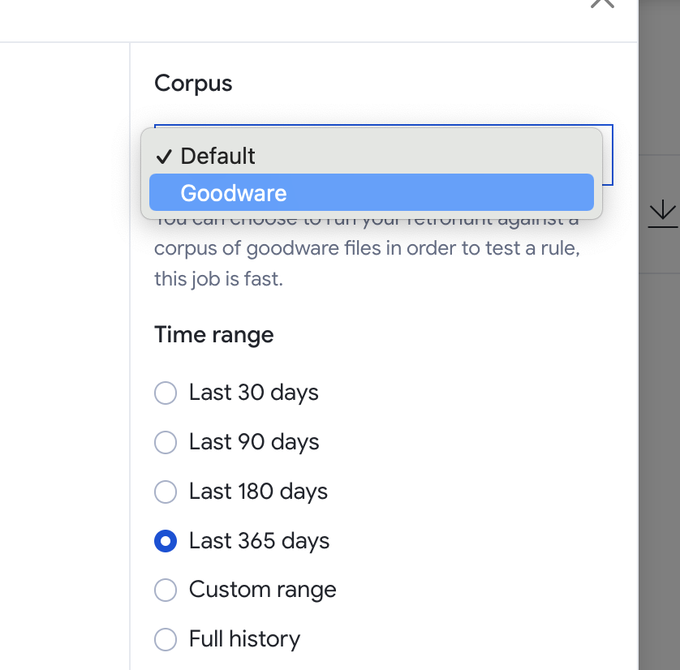
Sigma rules are one of the most powerful tools for Threat Hunters. Do you know that (for most cases) you can easily convert Sigma into LiveHunt/RetroHunt YARA rules? Find all the details here, by
@karlhiramoto
:
2
86
233
We found several samples we believe with high confidence are related to
@Mandiant
's DreamJob publication. Here is how we hunted them by
@alexey_firsh
:
1
72
230
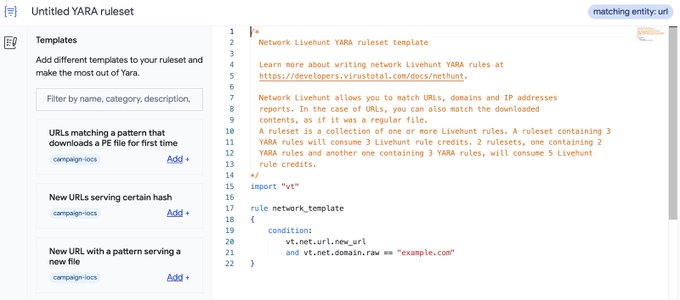
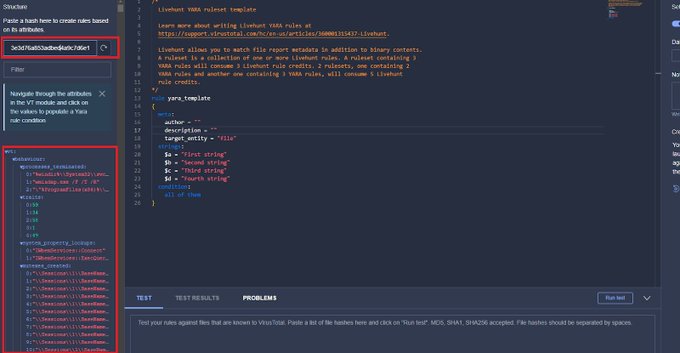
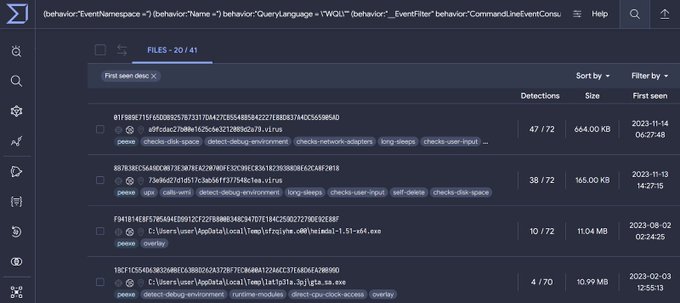
You can now automatically generate YARA LiveHunt rules for IOC tracking. Learn how, by
@leximagination
:
0
72
203
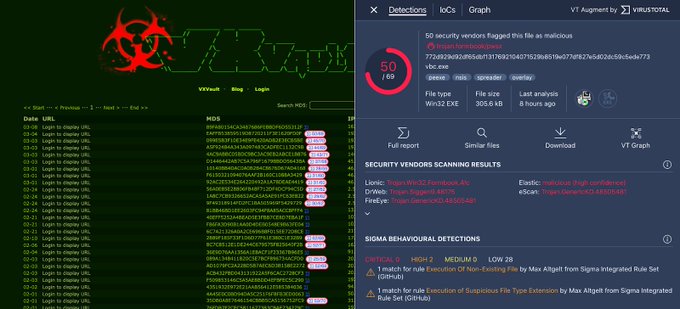
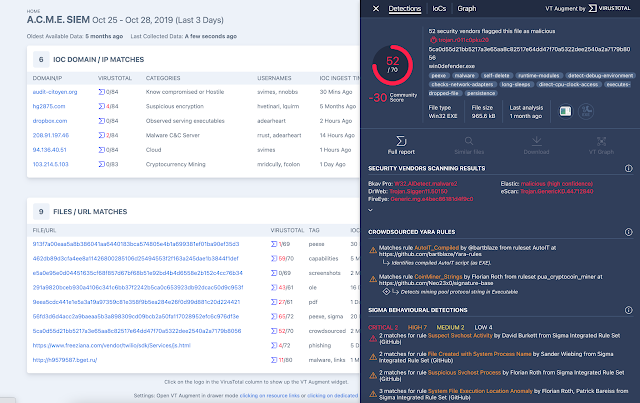
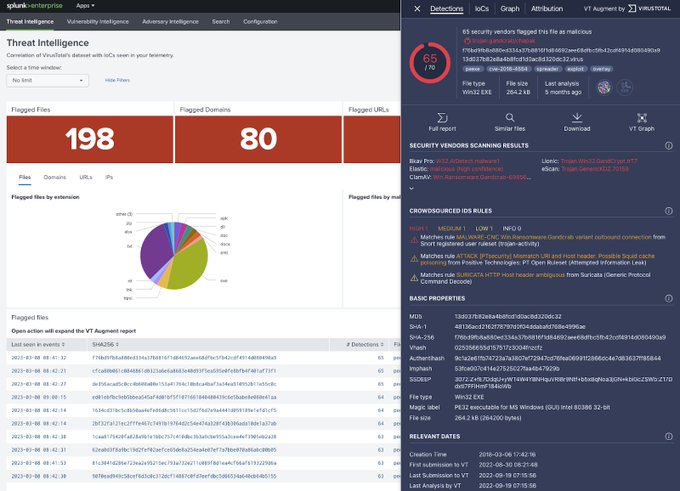
Today we are happy to introduce VT Augment, our widget to display VirusTotal context in 3rd-party products and services. Check all details in our blog post by
@zenitrame
3
61
181
16 years making a safer World, together.
Thank you all and happy
#ComputerSecurityDay
How it started | How it is going
6
35
177
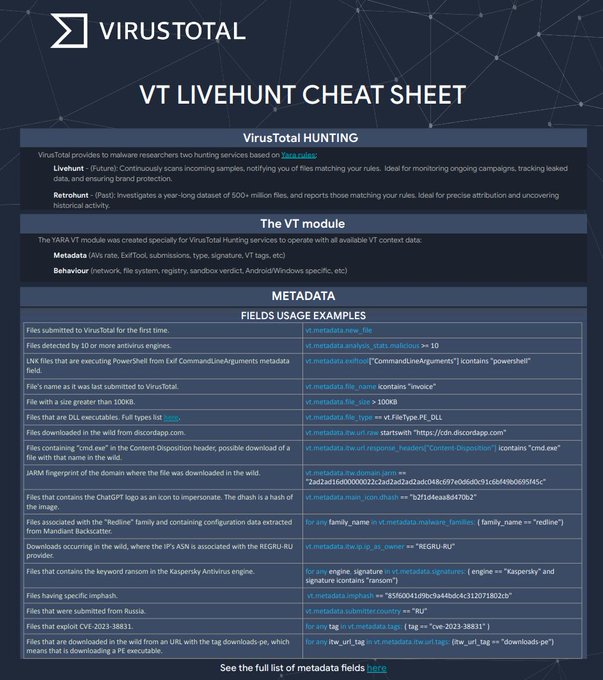
Need to get up and running your VT Livehunt rules? Our Cheat Sheet will streamline your monitoring rule creation. All details here, by
@ralcaz
:
2
60
172
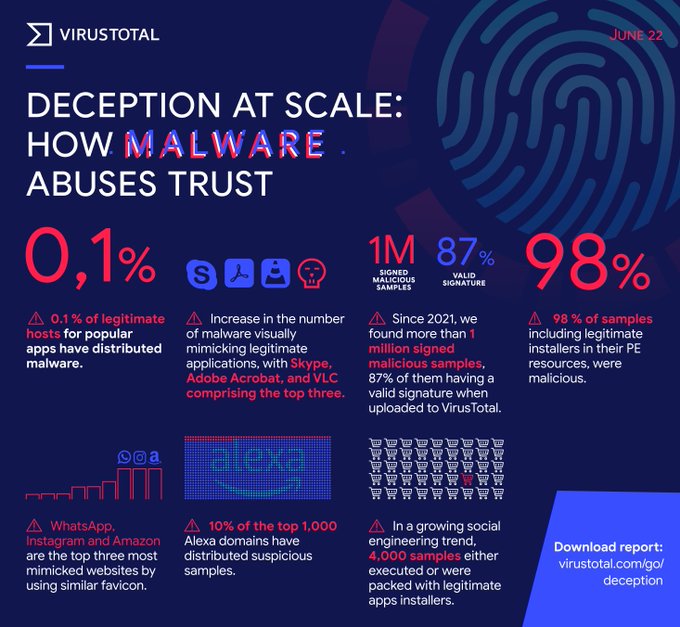
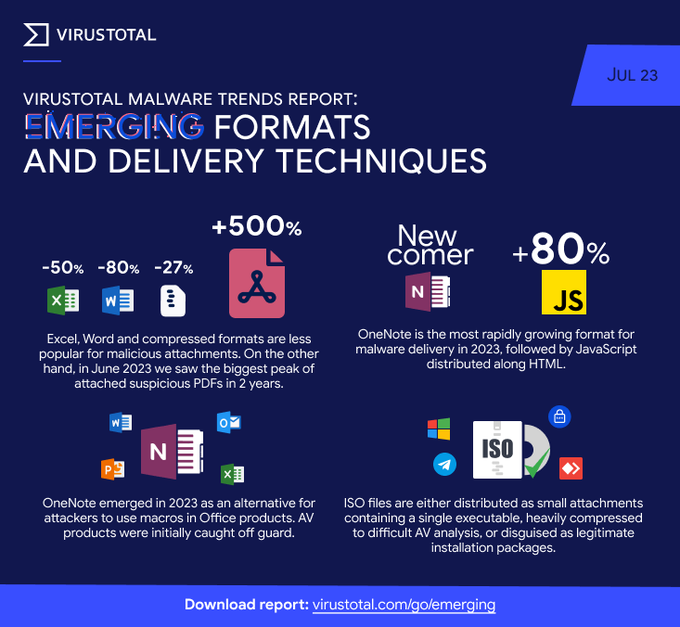
Our new VirusTotal Malware Trends Report: "Emerging formats and delivery techniques" is out! by
@gerardofn
,
@alexey_firsh
,
@entdark_
1
92
168
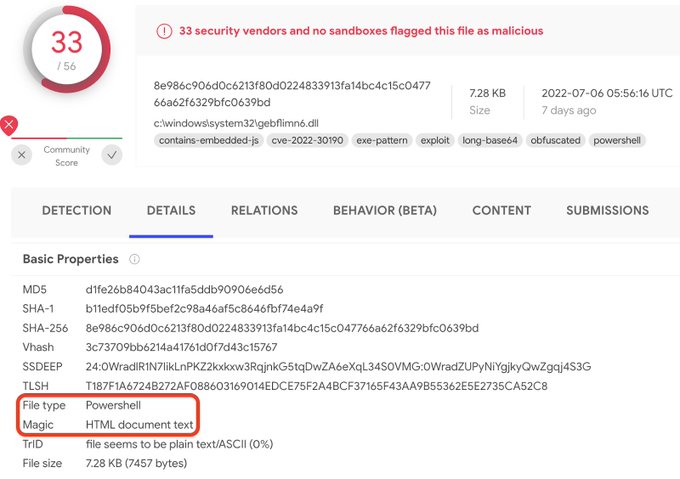
We hunted for samples exploiting CVE-2022-30190 (aka Follina) vulnerability. Here is what we learnt along with ideas to help how you hunt/monitor this and similar threats by yourself (by
@alexey_firsh
):
4
75
167
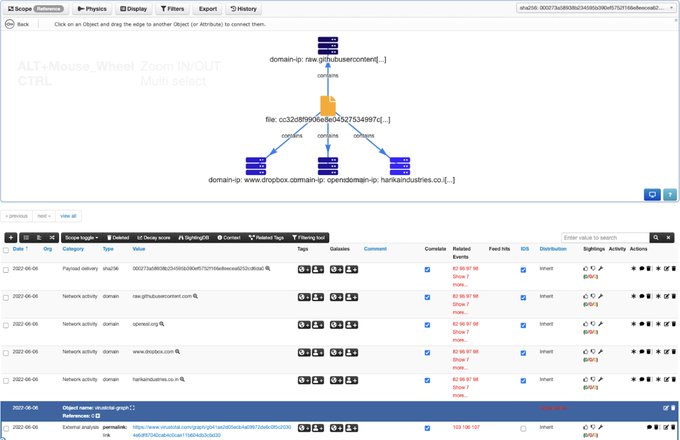
Good news for the
@MISPProject
's user community! Now you can export your VT Graph into a MISP event (Download as>MISP Event) including all relationships and (optionally) the VT report for all the indicators.
0
64
143
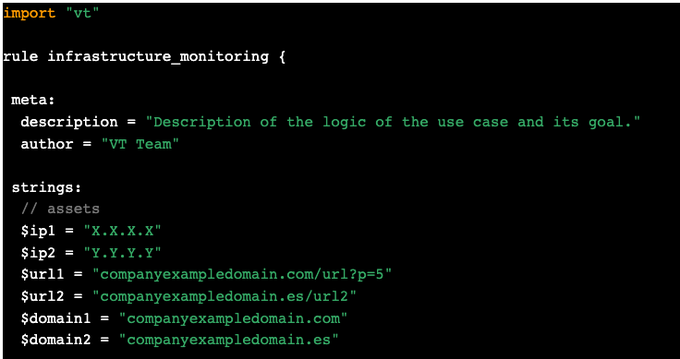
The definitive guide to monitor any suspicious activity in your infrastructure using VirusTotal (including examples and templates) is here:
by
@leximagination
0
44
142
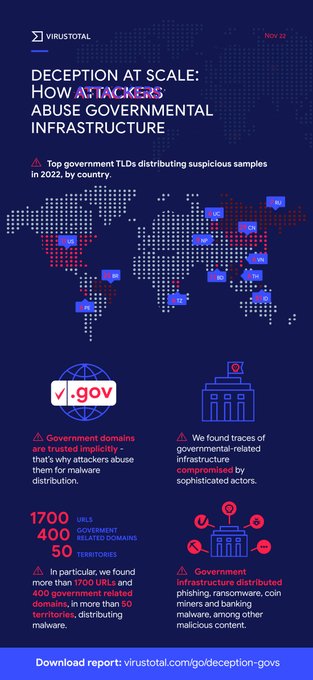
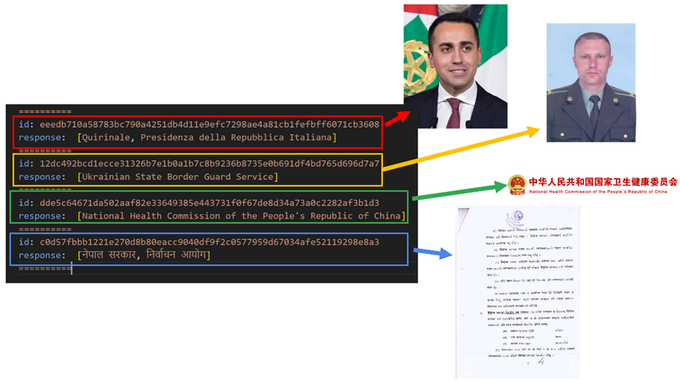
We have been analyzing how attackers abuse governmental infrastructure. You can find all details and several recent examples in our brand new report here:
by
@alexey_firsh
,
@entdark_
,
@gerardofn
and
@trompi
1
62
137
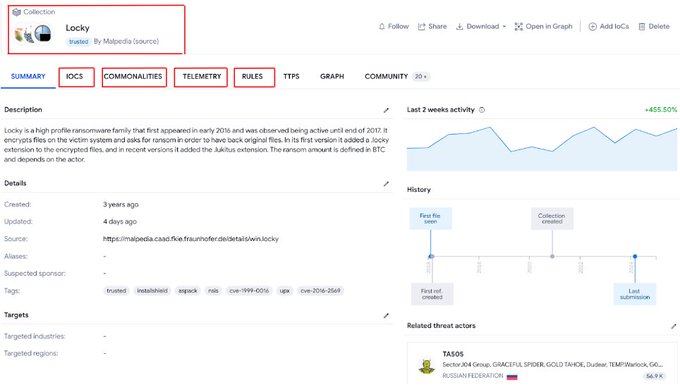
Today we are proud to introduce our brand new VirusTotal Collections! Discover, organise and save IOCs in a comprehensive way to make your research faster, easier and collaborative 🙌. Learn all about it in our blog by
@jinfantesd
:
0
57
139
Discover how we use Gemini 1.5 Pro to improve malware analysis! Gemini's capability to tackle up to 1 million tokens makes a difference, not only when facing huge macros, but also providing a way to automate analysis of decompiled code, by
@bquintero
:
2
34
139
We analyzed how attacks against financial institutions evolved in 2022. Check all details + examples on how you can monitor this activity by yourself here:
by
@gerardofn
0
67
133
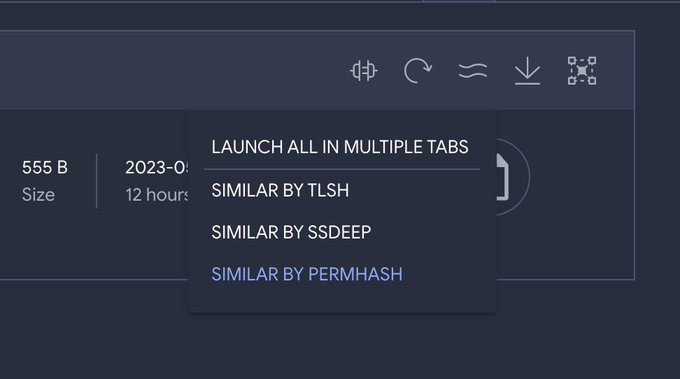
We've been working with
@Mandiant
's
@JWilsonSecurity
to add Permhash to VirusTotal, a new way to unearth adversary's infrastructure and toolkits by leveraging permissions similarity. Details here, by
@zenitrame
:
0
58
129
YARA is dead, long live YARA-X (ok, a bit too dramatic, but long live YARA-X!) by
@plusvic
:
1
35
125
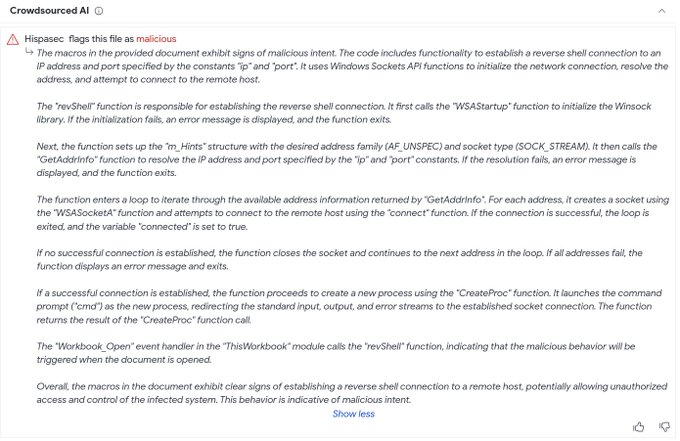
Today we launch VirusTotal's Crowdsourced AI, our open initiative for the security community to explore AI's capabilities to improve threat detection and response: by
@bquintero
1
65
119
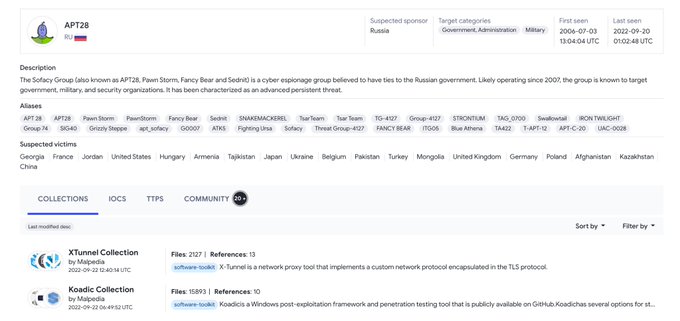
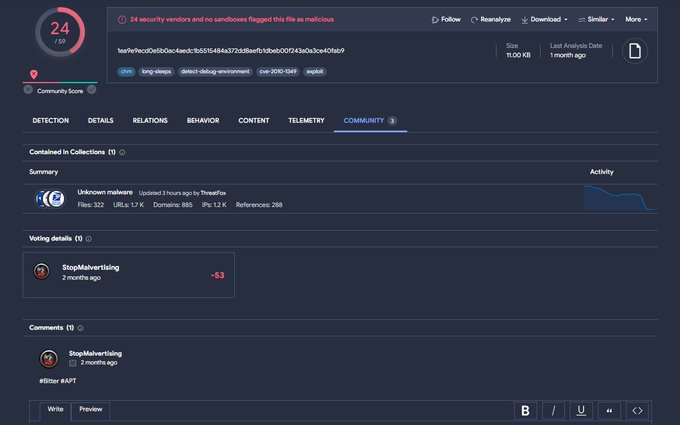
Hunt APTs by their images & artifacts! New blog on tracking adversaries using delivery-stage intel by
@Joseliyo_Jstnk
:
4
87
226
VirusTotal's role within Google Threat Intelligence and its continued dedication to the security community. Insights from founder
@bquintero
:
1
38
116
In case you missed our first "Hunting with VirusTotal" training, here you can find the recording, slides, and a very interesting Q&A: by
@alexey_firsh
. We hope to see you again in the next one!
0
46
105
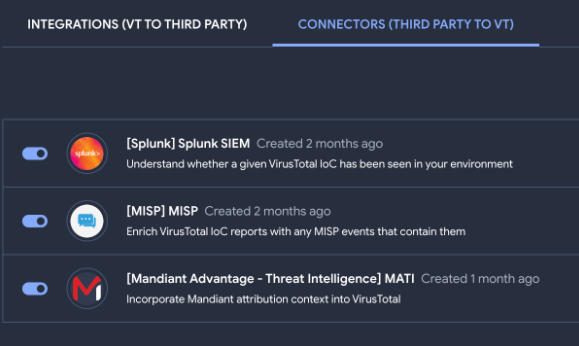
Introducing VirusTotal Connectors: unify threat context from multiple sources and get a comprehensive summary, all in a single place. All details here, by
@thetravelr
:
0
32
106
Code Insight has been one of our most impactful releases (thanks everyone!), but the VT team didn't stop working hard to improve it. Code Insight analyses now new formats, including BAT,CMD,SH and VBS. Find all details in our Q&A, by
@bquintero
:
1
37
105
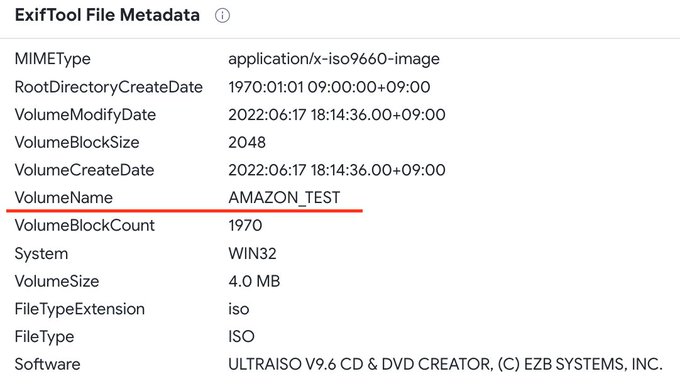
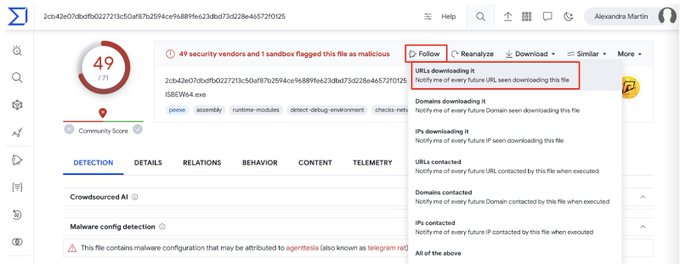
We found samples we suspect are related to
@Mandiant
Whatsapp phishing post: ISOs with similar content, OPSEC fails show discrepancies between volume path (with typo) inside the ISO and bait name. Please check our VT collection for more details:
2
37
104
Linux & macOS binaries? Covered! Our newest hunting feature allows matching Sigma rules against Linux and macOS samples, check our new post by
@Joseliyo_Jstnk
, including pro tips for crafting livehunt Yara rules based on Sigma:
2
37
102
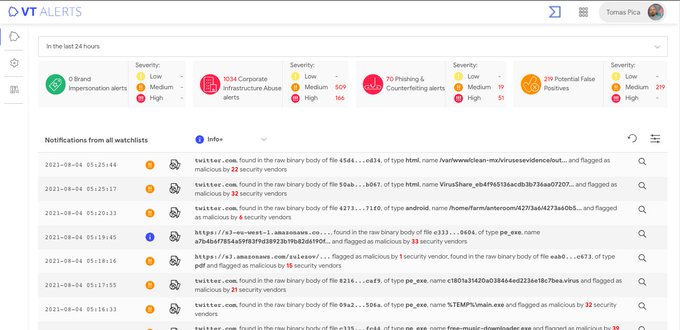
We are polishing final details! But if you can't wait to know more about VT Alerts (available next September), check "A sneak peek into VT Alerts" by
@TomasPica
:
0
42
100
VT Alerts, our anti-abuse and asset monitoring solution is finally here! Learn all about it in our latest blog post by
@TomasPica
1
44
100
Threat intelligence just got easier. Use VirusTotal Threat Landscape to track threat actors & prioritize threats. Our latest blog shows how CTI teams win, by
@ralcaz
:
4
38
100
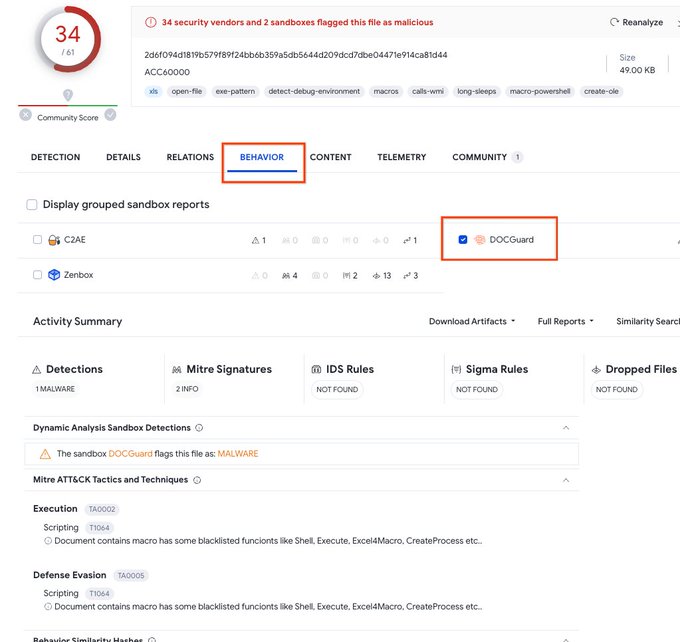
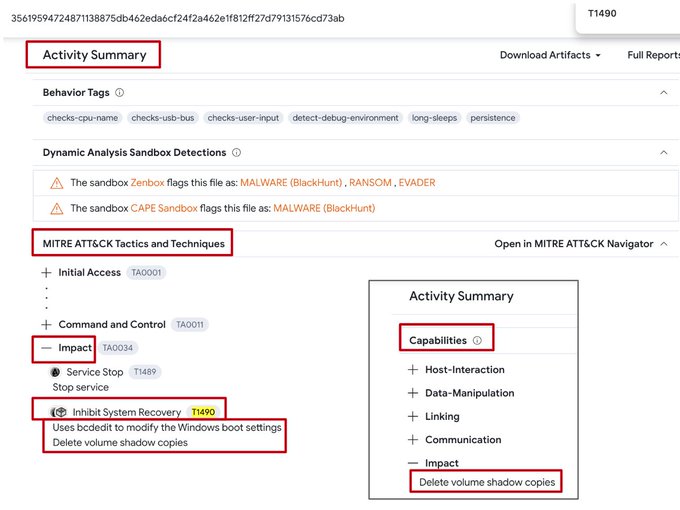
Harness TTPs for malware hunting! Our new blog post shows you how to leverage VirusTotal to hunt for ransomware, keyloggers & more, by
@leximagination
:
1
37
99
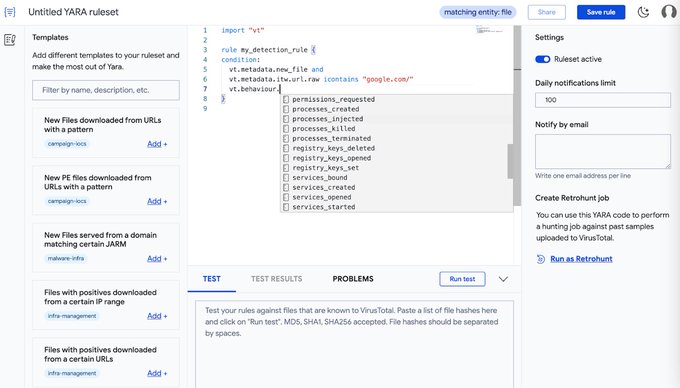
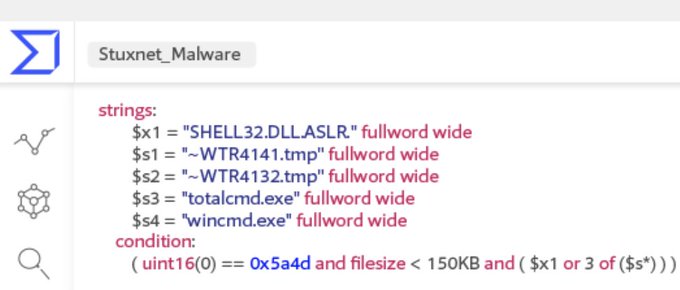
Syntax highlighting, auto-complete, templates, testing capabilities ... Our new YARA editor couldn't look better! Check out all the details here, by
@leximagination
:
1
40
96
We want to introduce our brand new “Known Distributors” attribute for file objects. We hope this will make your life easier, specially when dealing with false positives. Read all you need to know in our blogpost by
@Mrs_DarkDonado
:
3
52
93
Calling all security hunters! 📢
Want to know how to transform a VT Intelligence query into a Livehunt?
@Joseliyo_Jstnk
provides all the keys, including examples and best practices, in our latest blog post.
0
29
90
Our “Ransomware in a global context” report is finally out! Download it while it's hot
and find in our blog post (by Jesus and
@gerardofn
) tons of wonders to monitor ransom activity.
Don't forget to join us for our upcoming webinars to get all details!
1
38
83
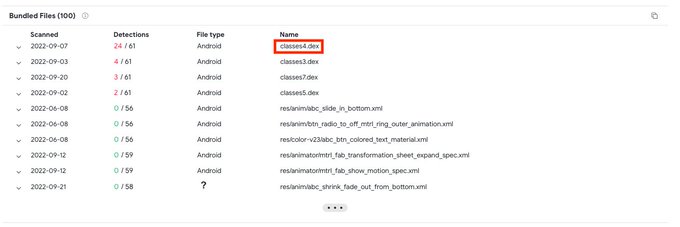
In our last blog post
@entdark_
describes, step by step, how from an unknown sample it is possible to monitor a whole new Android banking family:
1
36
85
Our friends from
@_CPResearch_
published on Zloader abusing CVE-2020-1599 in recent campaigns. Here you can learn how to leverage VirusTotal Intelligence to monitor malware abusing this vulnerability (by
@fcojsantos
)
0
28
83
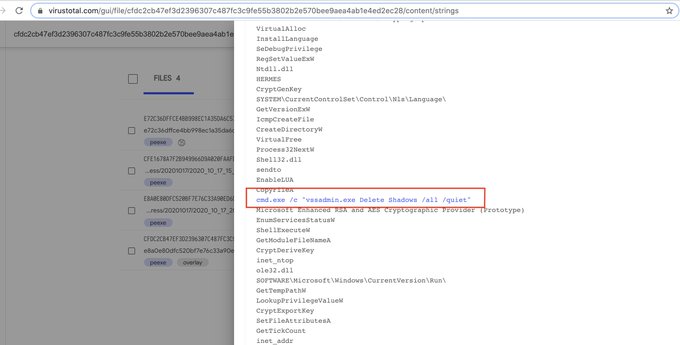
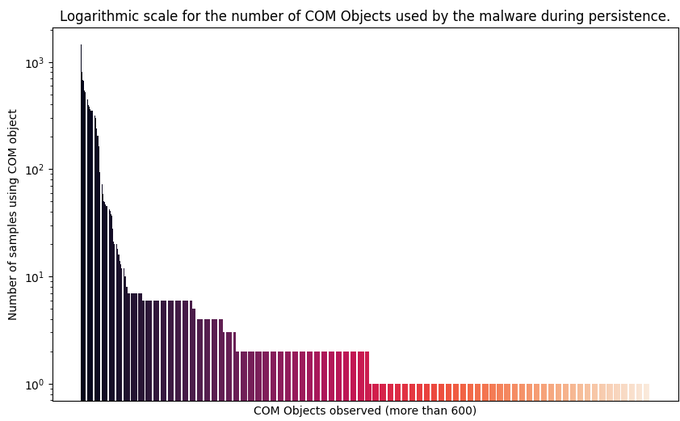
Threat actors actively leverage COM object hijacking for persistence and privilege escalation. We identified the most commonly abused COM objects and CLSIDs to help you stay safe by
@Joseliyo_Jstnk
:
2
39
79
Create YARA rules by clicking on observable properties. No need to remember VT YARA module by heart! by
@Joseliyo_Jstnk
0
28
75
@kaspersky
’s legend
@craiu
and VirusTotal's
@trompi
will be hosting our first “Applied YARA training” on August 31st. Make sure to book your seat!
2
36
75
Empower your threat hunting with actionable threat intel! 🕵️♀️
Discover how VTI queries based on third-party intel can enhance your understanding of malicious campaigns, streamline threat hunting, and automate threat monitoring, by
@Joseliyo_Jstnk
:
0
27
75
Crowdsourced Sigma rules play a key role in providing relevant context for your investigations.
Take a look to some ideas how to use them in our first blog post of the "Context is king" series by
@Mrs_DarkDonado
and
@trompi
:
0
28
69
At VirusTotal we ❤️ education!
We are happy to announce that will be providing access to VTIntelligence to students at
@LaSalleBCN
master in Cybersecurity.
2
10
65
At VirusTotal we ❤️ education!
We are very excited to announce our partnership with
@SANSInstitute
's
#SEC530
course co-authored by
@aboutsecurity
, providing students access to VTIntelligence to help them make TTPs actionable
0
16
64
We improved the identification of file formats using Generative AI. Find here all the details, by
@bquintero
:
2
28
62
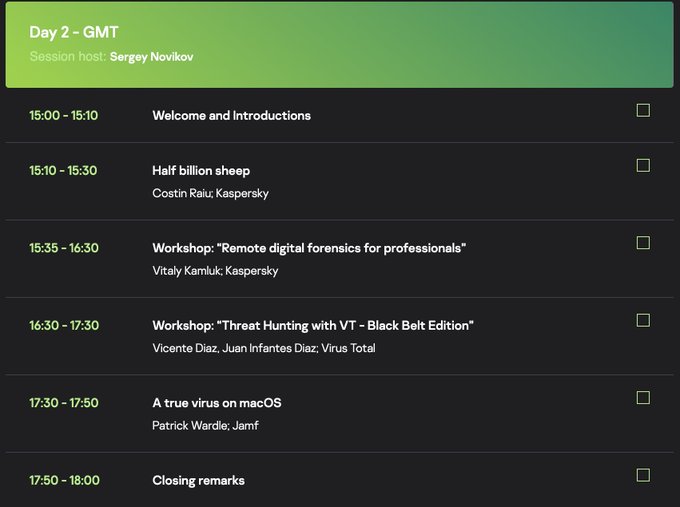
Join us today for our "Threat Hunting with VirusTotal - Black Belt edition" workshop
@TheSAScon
Day 2. Register here
0
27
60
Decentralized Domain Name Systems are abused to make malicious infrastructure resilient to take downs. Thanks to
@Mrs_DarkDonado
, now we have "alternative-dns" tag in VT when a domain uses such DNSs. You can read more in
@hispasec
una_al_dia (Spanish)
0
25
60
In our new post, "Unmasking Hidden Cyberthreats with Code Insight",
@bquintero
discusses real-world cases where AI-powered code analysis unveils malware, phishing attempts, and more:
1
32
61
We are proud to partner with
@TheSOCAcademy
to level up your threat analysis skills. Get more details on this course from its founder, Laura, in our latest blog:
0
12
60
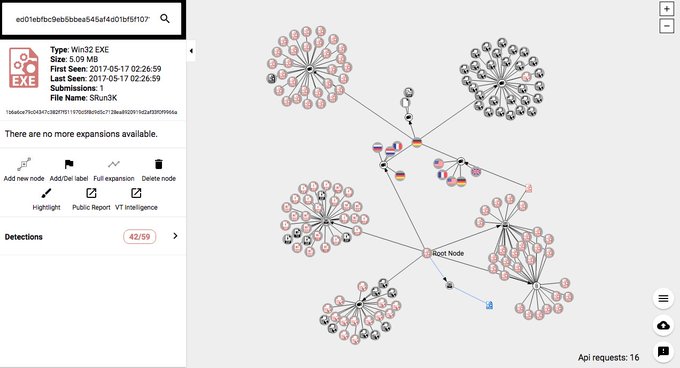
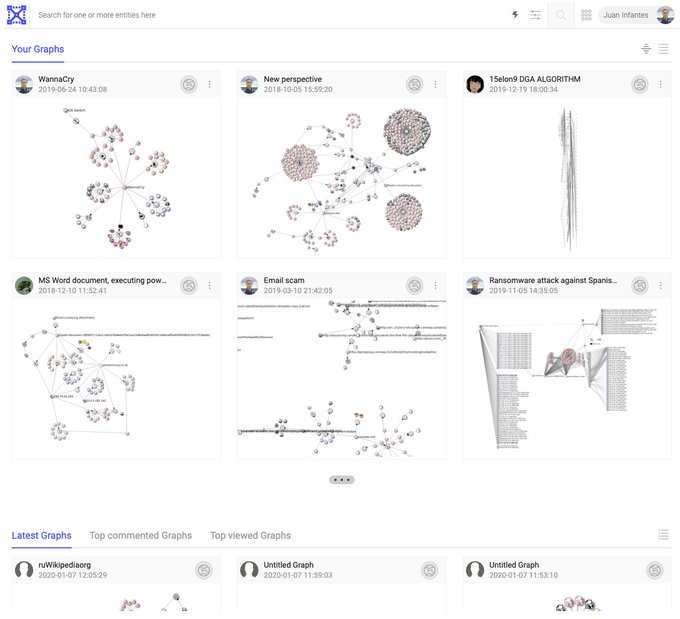
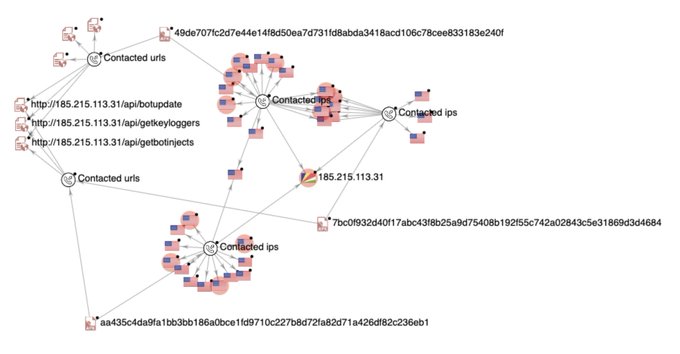
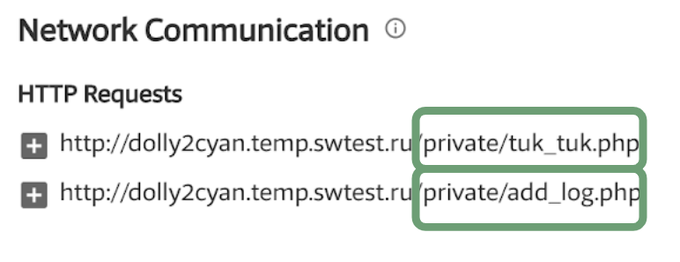
Visual investigations area an extremely useful resource for efficient evaluation of incidents. In our last post by
@jinfantesd
discover
1. how to use VTGraph from scratch, 2. cool examples of investigation, 3. amazing graphs by the community
1
20
54
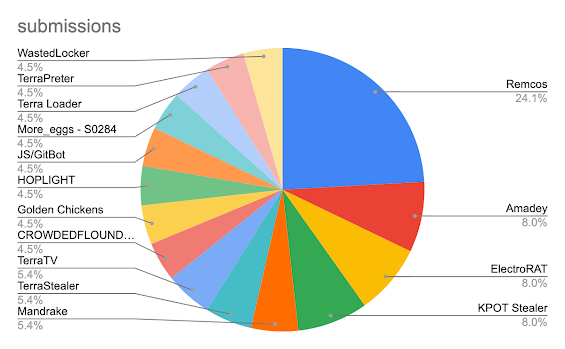
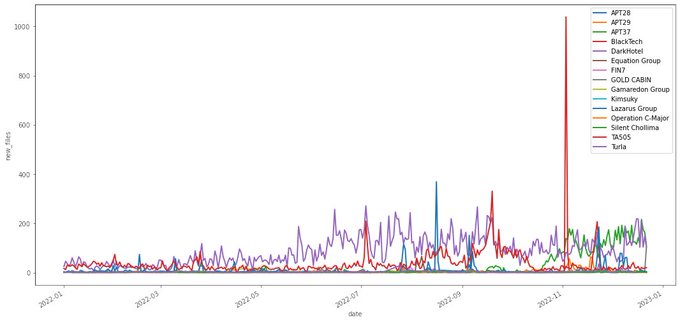
In 2022 we observed changes in how malware is distributed, rotation in exploitation techniques and we ranked victimology by industry and country. Check our summary of trends by
@gerardofn
:
0
45
59
We keep adding more security partners to our Crowdsourced AI effort. We are thrilled to welcome NICS Lab and their AI analysis engine for Powershell scripts, learn more about it at , by
@bquintero
1
25
55
Have you ever wondered how to build your brand new VT Collections using the command line? Learn all about it in our new post by
@jinfantesd
:
0
25
55
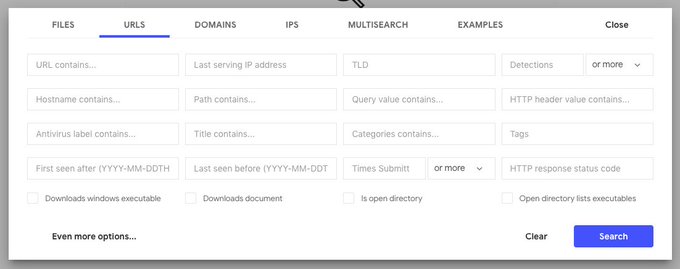
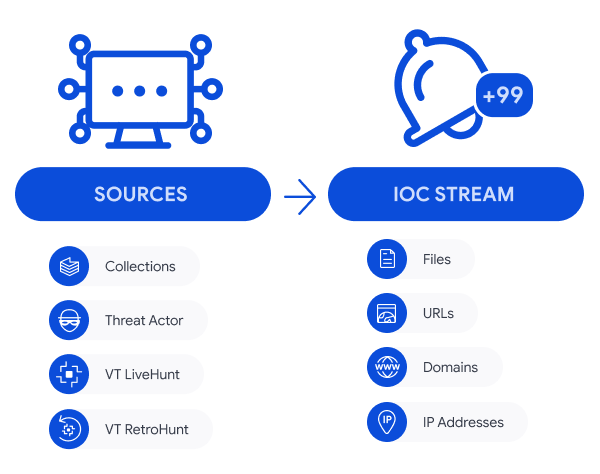
VirusTotal's IoC Stream is here to help you track campaigns and threat actors, letting you manage all related IOCs in a centralized repository for better visibility and ingestion. Find all details here, by
@leximagination
:
1
34
54